快速入门

本指南涵盖了Tailscale的所有功能:
- 入门 — 创建帐户并连接您的第一台设备
- 如何使用企业 VPN — 用零配置网状网络取代传统 VPN
- 如何使用安全远程访问 — 随时随地安全访问任何设备
- 如何使用站点到站点网络 — 无需硬件即可连接办公地点
- 如何使用多云网络 几分钟内即可连接 AWS、GCP 和 Azure
- 如何使用 Kubernetes — 使用网状网络保护您的集群
- 如何使用边缘计算和物联网部署 — 大规模管理远程设备
- 如何使用云连接 — 无需暴露端口即可访问云资源
- 如何使用安全人工智能 — 利用零信任网络保护 AI 工作负载
- How to Use Zero Trust Networking — Lock down access with identity-based controls
所需时间: 每部影片 5 分钟
本指南还包含以下内容: 专业提示 | 常见错误 | 故障排除 | 定价 | 替代方案
为什么信任本指南
I’ve used Tailscale for over a year and tested every feature covered here. This how to use Tailscale VPN 本教程源自真实的实践经验,而非营销噱头或供应商截图。
Tailscale is one of the most powerful mesh VPN tools available today.
但大多数用户仅仅触及了它功能的冰山一角。
本指南将向您展示如何使用所有主要功能。
一步一步教你,附带截图和专业技巧。
尾尺度教程
本 Tailscale 完整教程将一步一步地引导您了解每个功能,从初始设置到高级技巧,让您成为高级用户。

尾鳞
Connect all your 设备 into one secure private network in minutes. Tailscale builds on WireGuard encryption and works across every platform. Free for personal use with up to 3 users and 100 devices.
Tailscale入门指南
使用任何功能之前,请先完成此一次性设置。
大约需要3分钟。
请先观看这段简短的概述:
现在让我们一步一步来。
第一步:创建您的帐户
前往 tailscale.com 然后点击“开始使用”。
Tailscale uses single sign-on to authenticate users.
使用 Google、Microsoft、GitHub 或 Apple 帐户登录。
No new password needed — your existing account handles authentication.
✓ 检查点: 您应该可以看到Tailscale管理控制台。
步骤 2:下载并安装 Tailscale
从下载页面下载适用于您设备的 Tailscale。
它可在 Windows、macOS、Linux、iOS 和 安卓.
For a Linux machine, run this one-line install script in your terminal:
curl -fsSL https://tailscale.com/install.sh | sh
Apple devices can download the app from the App Store.
Log in with your account after installation.
这就是仪表盘的样子:
✓ 检查点: You should see your first device in the admin console.
Step 3: Connect a Second Device
在另一台设备上安装 Tailscale 并登录。
Both devices now share a private network called a tailnet.
Tailscale assigns each device IP addresses in the 100.x.x.x range.
MagicDNS also gives each device a human-readable hostname.
跑步 尾规模地位 in your terminal to see connected devices.
✅ 完成: You’re ready to use any feature below. Your tailnet devices can now communicate directly with encrypted connections.
如何使用 Tailscale Business VPN
商业 VPN 让您可以用零配置网状网络取代笨重的传统 VPN。
以下是使用步骤。
手表 商业 VPN in action:
现在让我们逐一分析每个步骤。
Step 1: Invite Your Team
打开管理控制台,然后转到“用户”选项卡。
使用贵公司的身份提供商发送邀请。
Each user installs the Tailscale client on their computer or phone.
Step 2: Configure Access Controls
转到管理控制台中的“访问控制”页面。
Define which users can access which machines and services.
Tailscale’s architecture uses identity-based rules instead of IP-based rules.
这就是它的样子:
✓ 检查点: You should see your ACL policy file in the admin console.
Step 3: Test Connectivity Between Devices
Ping a teammate’s device using its MagicDNS name.
Traffic routes over the shortest path possible between peers.
No central server sits between your encrypted connections.
✅ 结果: Your team now has a private network that works from anywhere in the world — no port forwarding or firewall changes needed.
💡 专业提示: Use Tailscale’s single-sign-on integration with your existing identity provider. When someone leaves the company, revoking their SSO access automatically removes their network access too.
如何使用 Tailscale 安全远程访问
安全的 远程访问 lets you reach any device from anywhere safely.
以下是使用步骤。
Watch Secure Remote Access in action:
现在让我们逐一分析每个步骤。
Step 1: Install Tailscale on Your Remote Device
Install Tailscale on the server or device you want to access remotely.
This could be a home network server, a Raspberry Pi, or an office computer.
Sign in so the device appears in your tailnet devices list.
Step 2: Connect from Any Location
Open the Tailscale app on your phone or laptop.
Your remote device shows up with its Tailscale IP address.
SSH into it, access a web server, or share files directly.
Tailscale 在后台自动处理 NAT 穿越。
✓ 检查点: You should be able to ping your remote device by name or IP.
Step 3: Enable Tailscale SSH (Optional)
Turn on Tailscale SSH to skip managing SSH keys.
跑步 tailscale up --ssh on the target machine.
Now you can SSH using just the device’s MagicDNS name.
✅ 结果: You can access your devices from anywhere without exposing services to the public internet.
💡 专业提示: Install Tailscale on a Raspberry Pi at home to create a permanent access point to your home network. You can access all other devices on the same domain through subnet routing.
如何使用 Tailscale 站点到站点网络
站点间联网 lets you connect office locations without dedicated hardware.
以下是使用步骤。
Watch Site-to-Site Networking in action:
现在让我们逐一分析每个步骤。
Step 1: Set Up Subnet Routers
Pick one device at each location to act as a subnet router.
Install Tailscale on it and run:
tailscale up --advertise-routes=192.168.1.0/24
Replace the IP range with your local network’s actual subnet.
Step 2: Approve the Routes
Open the admin console and find the device advertising routes.
Click “Approve” next to each advertised route.
Now all tailnet devices can reach machines on that subnet.
✓ 检查点: You should see “Subnet router” next to the device in your machines list.
Step 3: Connect Sites Together
Repeat steps 1 and 2 at each office location.
Devices at Site A can now access resources at Site B directly.
All traffic stays encrypted end-to-end between sites.
✅ 结果: Multiple office networks are now connected as one private network — no VPN appliances or complex router configurations needed.
💡 专业提示: Run subnet routers on always-on devices like a Linux machine or small server. A Raspberry Pi works perfectly for small offices and keeps your connectivity stable 24/7.
如何使用 Tailscale 多云网络
多云网络 lets you link AWS, GCP, and Azure servers in minutes.
以下是使用步骤。
Watch Multi-Cloud Networking in action:

现在让我们逐一分析每个步骤。
Step 1: Install Tailscale on Each Cloud Server
SSH into your cloud servers and install the Tailscale client.
Use the one-line install command for Linux:
curl -fsSL https://tailscale.com/install.sh | sh
跑步 tailscale up and authenticate each server.
Step 2: Verify Cloud Connectivity
Check tailscale status on each server to confirm they see each other.
Each cloud server gets a stable 100.x.x.x IP address on your tailnet.
Servers communicate directly with peer-to-peer encrypted connections.
✓ 检查点: You should see all cloud servers listed when you run tailscale status.
Step 3: Configure Access Between Clouds
Use ACLs to define which cloud servers can talk to which.
Tag servers by cloud provider for easy management.
Packets flow directly between clouds without touching the public internet.
✅ 结果: Your AWS, GCP, and Azure servers now communicate as if they’re on the same local network.
💡 专业提示: Use Tailscale’s DNS features to give cloud servers human-readable names. Instead of remembering IP addresses across providers, just use names like db-primary 或者 api-west.
如何使用 Tailscale Kubernetes
Kubernetes integration lets you secure your clusters with mesh networking.
以下是使用步骤。
Watch Kubernetes in action:

现在让我们逐一分析每个步骤。
Step 1: Deploy the Tailscale Operator
Install the Tailscale Kubernetes operator in your cluster.
Use Helm to deploy it with a single command.
The operator manages Tailscale connections for your pods and services.
步骤 2:将服务暴露给您的尾网
Add Tailscale annotations to your Kubernetes service definitions.
Services become accessible to your tailnet devices automatically.
No LoadBalancer or public IP address needed for internal access.
✓ 检查点: You should see your Kubernetes services in the admin console machines list.
Step 3: Set Up Ingress for External Access
Configure Tailscale Funnel if you need to expose a service to the internet.
Otherwise, keep services private and accessible only through your tailnet.
Use ACL tags to control which users can reach which cluster resources.
✅ 结果: Your Kubernetes services are now accessible through your private network without exposing them to the wider internet.
💡 专业提示: Use the Tailscale operator’s egress feature to let pods connect to other tailnet devices. This is perfect for accessing databases or services running outside your cluster.
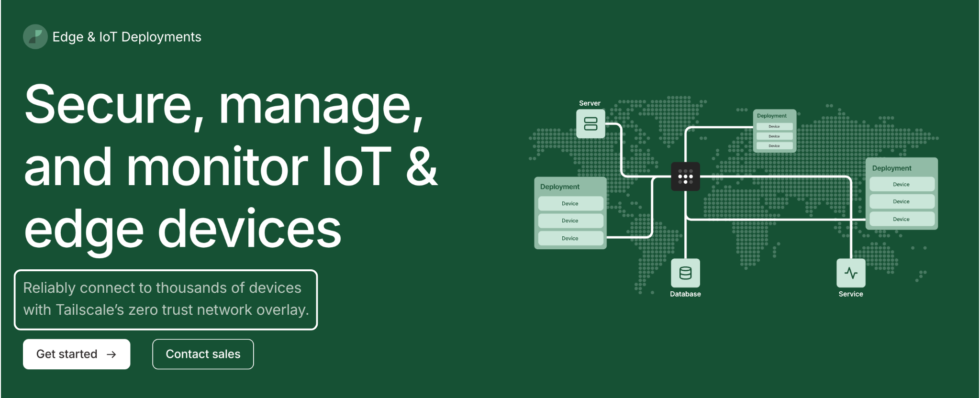
如何使用 Tailscale Edge 和物联网部署
边缘计算和物联网部署 lets you manage remote devices at scale.
以下是使用步骤。
Watch Edge & IoT Deployments in action:
现在让我们逐一分析每个步骤。
步骤 1:在边缘设备上安装 Tailscale
Deploy Tailscale on each IoT device or edge node.
Tailscale runs on Raspberry Pi, ARM-based boards, and embedded Linux.
Use the one-line script to install it on any Linux machine.
Step 2: Manage Devices from the Admin Console
All installed devices appear in your machines list automatically.
按位置、功能或部署组标记设备。
Use ACLs to restrict which devices can communicate with each other.
✓ 检查点: You should see all your IoT devices listed as connected in the admin console.
Step 3: Access Devices Remotely
SSH into any edge device from your laptop or phone.
No need to open ports on your firewall or configure port forwarding.
Tailscale connects you directly using NAT traversal techniques.
✅ 结果: You can monitor and manage hundreds of remote IoT devices from anywhere without exposing them to the public internet.
💡 专业提示: Use auth keys for headless device enrollment. Generate keys in the admin console and pass them during installation so devices join your tailnet automatically without manual login.
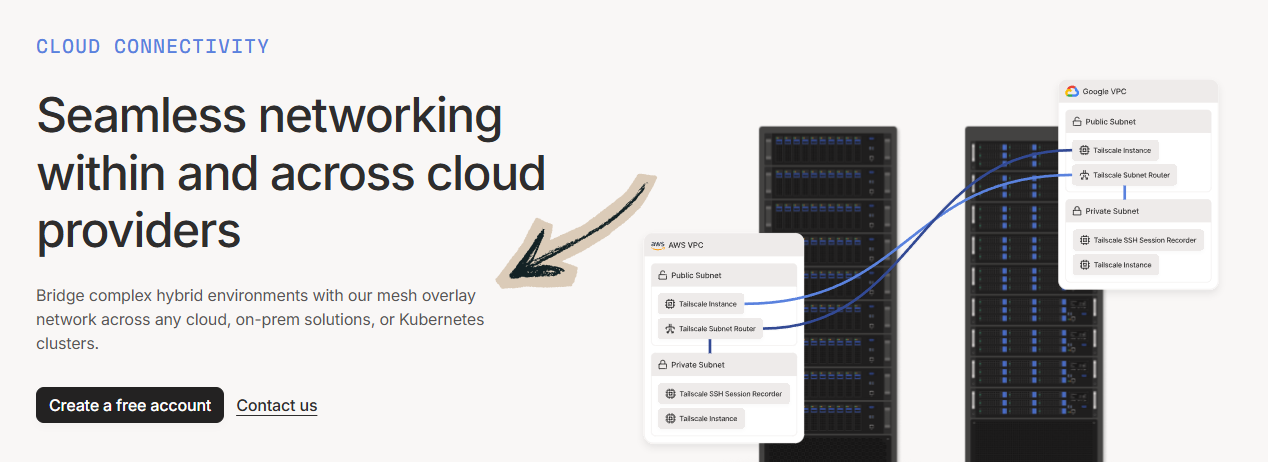
如何使用 Tailscale 云连接
云连接 lets you access cloud resources without exposing ports.
以下是使用步骤。
Watch Cloud Connectivity in action:
现在让我们逐一分析每个步骤。
步骤 1:在云实例上安装 Tailscale
将 Tailscale 添加到您的云虚拟机、容器或无服务器函数中。
The client installs in seconds on any Linux-based cloud instance.
Each instance gets a private Tailscale IP address on your tailnet.
步骤二:移除公网端口
Close all public-facing ports on your cloud instances.
Access everything through Tailscale’s private network instead.
Your cloud services become accessible only to authenticated tailnet members.
✓ 检查点: Verify your cloud services are no longer accessible from the public internet.
Step 3: Access Cloud Resources from Any Device
Open your Tailscale app and connect to your cloud instance by name.
Access databases, dashboards, and APIs without VPN tunnels.
Traffic is fully encrypted between your device and the cloud.
✅ 结果: Your cloud infrastructure is now private and accessible only through your secure tailnet.
💡 专业提示: Use Tailscale Funnel to selectively expose specific services (like a web server) to the public internet while keeping everything else private. It gives you control over what the outside world can see.
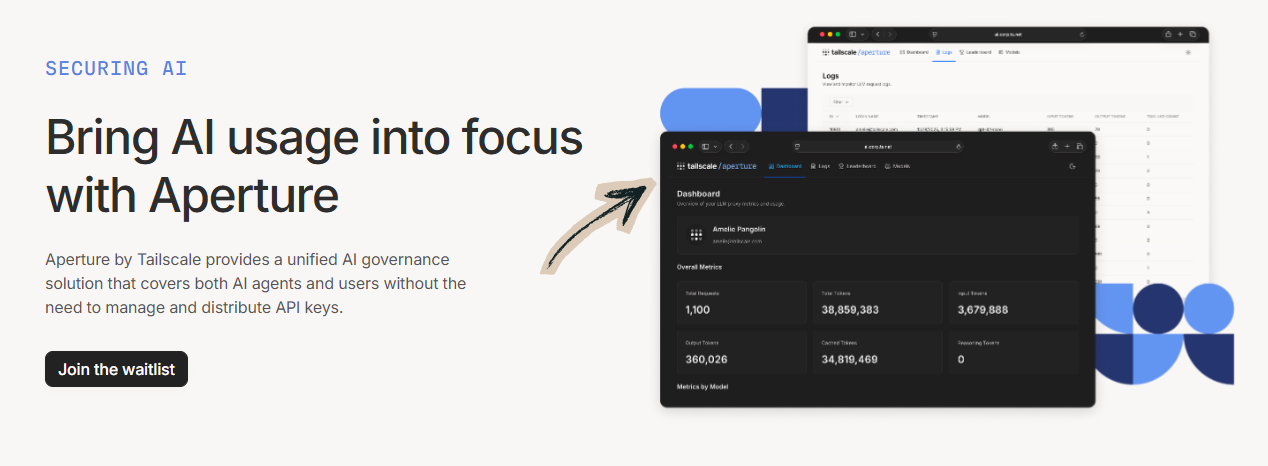
如何使用 Tailscale 保障人工智能
保障人工智能安全 lets you protect AI workloads with zero trust networking.
以下是使用步骤。
Watch Securing AI in action:
现在让我们逐一分析每个步骤。
Step 1: Connect Your AI Infrastructure
Install Tailscale on GPU servers, training nodes, and inference endpoints.
Each node joins your tailnet and gets a stable IP address.
This works whether your AI runs on-premise or across multiple cloud providers.
Step 2: Restrict Access to AI Resources
Use ACL policies to control who can access your AI models and 数据.
Only authorized users and services can reach training pipelines.
Keep model weights and datasets off the public internet.
✓ 检查点: Verify that only tagged AI-team members can reach your GPU nodes.
Step 3: Monitor and Audit AI Access
Enable network flow logging in the admin console.
Track who accesses your AI infrastructure and when.
Use audit logs to meet compliance and security requirements.
✅ 结果: Your AI workloads are now protected behind a zero trust network — no unauthorized access possible.
💡 专业提示: Tag your GPU servers and data stores separately in ACLs. This way, data scientists can access notebooks but not production inference endpoints — and vice versa for your operations team.
如何使用 Tailscale 零信任网络
零信任网络 lets you lock down access with identity-based controls.
以下是使用步骤。
Watch Zero Trust Networking in action:
现在让我们逐一分析每个步骤。
Step 1: Define Your Access Policy
Open the ACL editor in the admin console.
Write rules that specify exactly who can access which resources.
Every connection must be authenticated — no default trust.
Step 2: Apply Device-Level Controls
Tag each device based on its role (for example, tag:server 或者 tag:dev).
在 ACL 规则中使用标签可以大规模管理访问权限。
Tailscale checks both user identity and device identity before allowing traffic.
✓ 检查点: Try accessing a restricted resource from an unauthorized device — it should be blocked.
Step 3: Enable Logging and Alerts
Turn on configuration audit logging and network flow logs.
Stream logs to your SIEM tool for real-time monitoring.
Set up alerts for unauthorized access attempts.
✅ 结果: Your network now enforces zero trust — every connection is verified, and nothing is trusted by default.
💡 专业提示: Start with a permissive ACL policy and gradually tighten it. Review your network flow logs to understand actual traffic patterns before locking down access. This prevents accidentally blocking legitimate connections.
Tailscale 专业技巧和快捷方式
经过一年多的Tailscale测试,以下是我总结的最佳技巧。
键盘快捷键
| 行动 | 命令 |
|---|---|
| 检查连接状态 | 尾规模地位 |
| Connect to your tailnet | tailscale up |
| Disconnect from tailnet | tailscale down |
| Ping a peer device | tailscale ping [hostname] |
| Send a file via Taildrop | tailscale 文件 cp [文件] [设备]: |
| Receive files via Taildrop | tailscale file get . |
| 查看您的 Tailscale IP 地址 | 尾部规模 IP |
| Enable exit node | tailscale up --exit-node=[hostname] |
大多数人错过的隐藏功能
- Taildrop 文件共享: Send files directly between devices without using the cloud. Just drag and drop from one device to another — all data transfers are fully encrypted.
- 出口节点: Route all your internet traffic through a specific device on your tailnet. Set up an exit node at home, and your phone’s traffic looks like it’s coming from your home network — even from a coffee shop.
- MagicDNS Custom Search Domains: Add a custom search domain so you can type just the hostname instead of the full DNS name. For example, type
myserverinstead ofmyserver.tailnet-name.ts.net. - Tailscale Funnel: Expose a local web server to the public internet through Tailscale’s network. No port forwarding needed — just run one command and your service is accessible by anyone with the URL.
尾部规模分析中需要避免的常见错误
Mistake #1: Thinking Tailscale Hides Your IP from Websites
❌ 错误: Using Tailscale as a traditional VPN to hide your IP address from websites or unblock streaming services.
✅ 右图: Tailscale is a mesh networking tool for connecting your own devices. If you need to mask your public IP, use a traditional VPN service or set up an exit node through a cloud server.
Mistake #2: Not Approving Subnet Routes
❌ 错误: Advertising subnet routes on a device but forgetting to approve them in the admin console, then wondering why connectivity fails.
✅ 右图: Always check the admin console after advertising routes. Click “Approve” for each route. Without approval, other devices cannot reach the advertised subnet.
Mistake #3: Using a Work Email for Personal Use
❌ 错误: Signing up with your work email (@company.com) for personal projects, then losing access when you leave the company.
✅ 右图: Use a personal email (Gmail, GitHub, Apple) for personal use. Tailscale ties your tailnet to the email domain — using a work email means your company controls the account.
尾尺度故障排除
Problem: Devices Not Connecting to Each Other
原因: Firewalls or network restrictions may block the UDP traffic Tailscale needs. Some corporate networks and public Wi-Fi networks restrict peer-to-peer connectivity.
使固定: 跑步 tailscale netcheck to test your network. If direct connections fail, Tailscale falls back to relay servers called DERPs. Check that UDP port 41641 is not blocked. Also try switching networks to confirm the issue is network-specific.
Problem: MagicDNS Names Not Resolving
原因: MagicDNS might not be enabled, or your device’s DNS configuration may override Tailscale’s settings.
使固定: Go to the DNS settings in the admin console and verify MagicDNS is turned on. On Linux, check that /etc/resolv.conf points to Tailscale’s DNS. Restart the Tailscale service if DNS changes don’t take effect.
问题:出口节点未路由流量
原因: The exit node might not be properly configured or approved. IP forwarding may also be disabled on the exit node device.
使固定: 跑步 tailscale up --advertise-exit-node on the device you want as an exit node. Then approve it in the admin console. On Linux, enable IP forwarding with echo 1 > /proc/sys/net/ipv4/ip_forward. Verify with 尾规模地位 to confirm the node is active.
📌 笔记: If none of these fix your issue, check Tailscale’s documentation at tailscale.com/kb or contact Tailscale support.
Tailscale是什么?
尾鳞 is a mesh VPN tool that creates a decentralized private network between your devices.
Think of it like a secret tunnel that connects all your computers, phones, and servers — no matter where they are in the world.
Tailscale is based on the WireGuard VPN protocol and is built by a company headquartered in San Francisco and Toronto.
Unlike traditional VPNs that route all traffic through a central server, Tailscale routes traffic over the shortest path possible.
It establishes direct peer-to-peer connections between your devices whenever it can.
If a direct connection cannot be established, Tailscale uses relay servers called DERPs to keep you connected.
Tailscale assigns IP addresses in the 100.x.x.x range to every device on a tailnet.
This lets all your tailnet devices communicate directly with each other over encrypted connections.
Tailscale is free for personal use and evaluation for up to 3 users on a single tailnet with a limit of 100 devices.
Setting up Tailscale generally takes just a few minutes across all major platforms.
Tailscale automatically handles IP addressing and public key management between devices.
The MagicDNS feature automatically assigns human-readable hostnames to devices so you don’t need to remember IP addresses.
You can use Tailscale to connect devices that are behind NAT without complex configurations.
Tailscale provides a web interface for managing all your devices on the tailnet through the admin console.
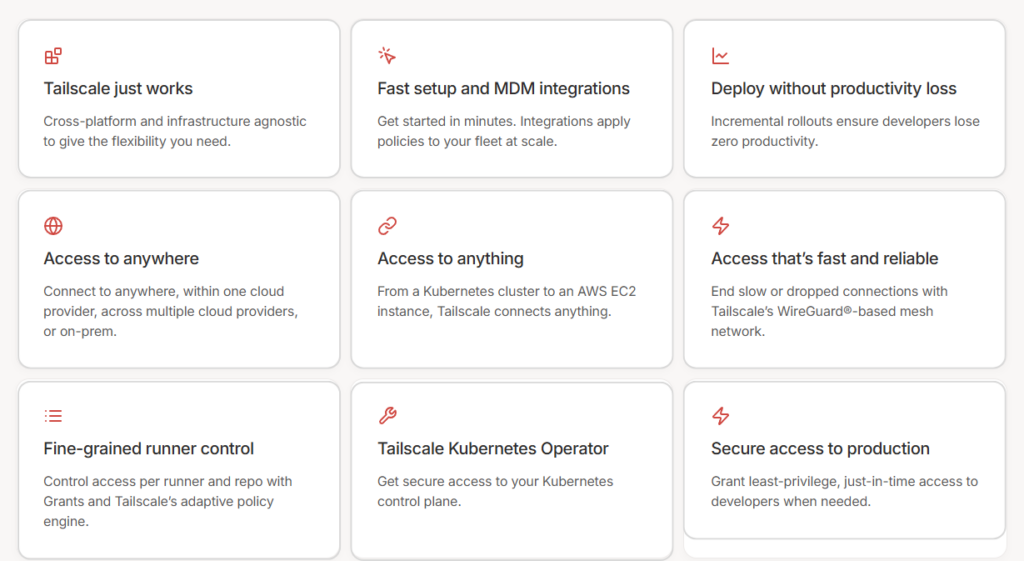
它包含以下主要特点:
- 企业VPN: Replace traditional VPN with a zero-config mesh network for your team.
- 安全远程访问: Reach any device from anywhere without opening firewall ports.
- 站点间联网: Connect multiple office networks using subnet routers.
- 多云网络: Link servers across AWS, GCP, and Azure 即刻.
- Kubernetes: Secure your Kubernetes clusters with mesh networking.
- 边缘计算和物联网部署: Manage Raspberry Pi and IoT devices at scale.
- 云连接: Access cloud resources privately without public ports.
- 保障人工智能安全: Protect AI workloads with identity-based access controls.
- 零信任网络: Enforce least-privilege access across your network.
如需完整评测,请参阅我们的 Tailscale 评测.

尾量定价
以下是Tailscale在2026年的成本:
| 计划 | 价格 | 最适合 |
|---|---|---|
| 个人的 | Free (up to 3 users, 100 devices) | Individuals and home lab enthusiasts |
| 个人加强版 | $5/month (up to 6 users, 100 devices) | Families and small groups sharing a network |
| 起动机 | 每用户每月 6 美元 | Small teams replacing a traditional VPN |
| 优质的 | 每用户每月 18 美元 | Growing teams needing SSO, ACLs, and audit logs |
| 企业 | 定制定价 | 有合规需求的大型组织 |
免费试用: Yes — the Personal plan is free forever. Business plans include a 14-day trial with no user limit.
退款保证: Tailscale does not advertise a specific refund policy. Contact support for billing inquiries.
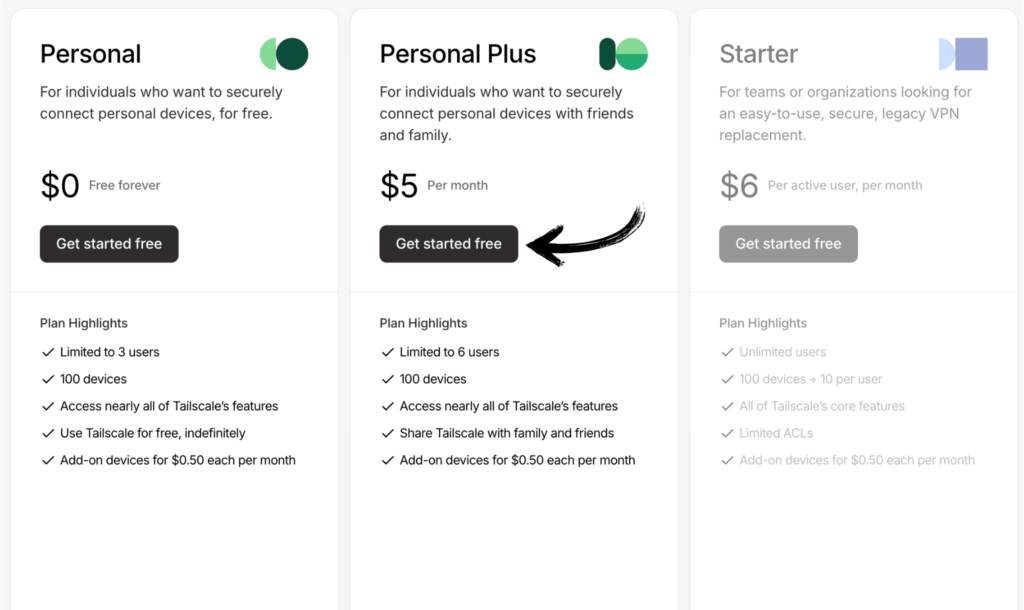
💰 性价比最高: Personal plan — it includes nearly every Tailscale feature for free. Most personal users never need to upgrade. Add more devices and users as your needs grow.
Tailscale 与其他方案的比较
Tailscale 的表现如何?以下是竞争格局:
| 工具 | 最适合 | 价格 | 等级 |
|---|---|---|---|
| 尾鳞 | Mesh networking & remote access | Free / $5/mo+ | ⭐ 4.7 |
| NordVPN | Online privacy & streaming | 每月 2.99 美元 | ⭐ 4.5 |
| ExpressVPN | Speed & global server coverage | 每月 2.44 美元 | ⭐ 4.6 |
| PureVPN | 经济实惠的隐私 | 每月 2.15 美元 | ⭐ 4.0 |
| 冲浪鲨 | 无限设备连接 | 每月 1.99 美元 | ⭐ 4.4 |
| ProtonVPN | 隐私优先,提供免费套餐 | 免费/每月 2.99 美元 | ⭐ 4.5 |
| 网络幽灵 | 流媒体和种子下载 | 每月 2.03 美元 | ⭐ 4.3 |
| 私人互联网接入 | Customizable security | 每月 2.03 美元 | ⭐ 4.2 |
快速精选:
- 综合最佳: Tailscale — unmatched for device-to-device networking with a generous free plan.
- 最佳预算: Surfshark — unlimited devices at $1.99/month with strong privacy.
- 最适合初学者: NordVPN — simple apps and one-click server connections.
- 最注重隐私: ProtonVPN — Swiss-based with a strong free tier and no-logs policy.
🎯 尾规模替代方案
正在寻找 Tailscale 的替代方案?以下是一些最佳选择:
- 🚀 NordVPN: Over 6,400 servers in 111 countries. Best for hiding your IP address, streaming geo-blocked content, and general online privacy.
- ⚡ ExpressVPN: Consistently fast speeds across the world. Great for users who want reliable performance and easy-to-use apps on every platform.
- 💰 PureVPN: Affordable plans starting at $2.15/month. Includes port forwarding for direct device connections and a large server network.
- 🌟 Surfshark: Unlimited device connections on every plan. Great for families and users with many devices who want privacy protection.
- 🔒 ProtonVPN: Swiss-based with a strong no-logs policy and a free tier. Best for users who prioritize privacy above everything else.
- 🧠 PrivadoVPN: Budget-friendly at $1.11/month for a 2-year plan. Includes a free tier with 10GB of monthly data for basic use.
- 🔧 AdGuard VPN: Built-in ad and tracker blocking alongside VPN protection. Works well for users who want privacy and ad-free browsing in one app.
- 🏢 虚拟护盾: Simple interface with always-on protection. Designed for non-technical users who want set-and-forget VPN security.
- ⭐ StrongVPN: Reliable connections with no data caps. Good for users who need a basic, no-frills VPN with consistent performance.
- 🎯 AuraVPN: Part of the Aura digital safety suite. Includes VPN, antivirus, and identity theft protection in one subscription.
- 👶 网络幽灵: Dedicated servers for streaming and torrenting. One of the easiest VPNs to use with a 45-day money-back guarantee.
- 💼 麦卡菲 VPN: Bundled with McAfee’s antivirus and identity monitoring. Good for users who want an all-in-one security package.
- 📊 私人互联网接入: Highly customizable with open-source apps. Great for technical users who want full control over their VPN settings.
- 🔥 神秘: Decentralized VPN powered by a peer-to-peer network. Unique architecture for users interested in blockchain-based privacy.
- 🛡️ SafeShell VPN: Focused on bypassing internet restrictions in censored regions. Good for users in countries with heavy internet filtering.
- 🐚 Oyster VPN: Lifetime access option at a low one-time price. Good for budget-conscious users who want long-term VPN coverage.
完整列表请参见我们的 Tailscale alternatives 指导。
⚔️ Tailscale 对比
以下是Tailscale与各竞争对手的对比情况:
- Tailscale 对比 NordVPN: Tailscale creates a zero-trust private network between your devices. NordVPN hides your IP and unblocks streaming. Choose NordVPN for browsing privacy, Tailscale for remote access.
- Tailscale 与 ExpressVPN 对比: ExpressVPN is faster for general browsing with servers in 105 countries. Tailscale wins for device-to-device networking and team collaboration with no central server.
- Tailscale 对比 PureVPN: PureVPN offers port forwarding and a large server network for privacy. Tailscale provides direct mesh connections and is better for accessing your own machines remotely.
- Tailscale 对阵 Surfshark: Surfshark gives unlimited connections and streaming access. Tailscale connects devices directly with no central server. Choose Surfshark for streaming, Tailscale for networking.
- Tailscale 对比 ProtonVPN: ProtonVPN is Swiss-based with strong anonymity tools. Tailscale focuses on connecting devices. ProtonVPN wins for browsing privacy, Tailscale for remote device access.
- Tailscale 对比 PrivadoVPN: PrivadoVPN is a budget-friendly traditional VPN. Tailscale connects your own devices in a mesh. PrivadoVPN is better for hiding IP addresses, Tailscale for device management.
- Tailscale VPN 对比 AdGuard VPN: AdGuard VPN blocks ads and trackers alongside VPN encryption. Tailscale focuses purely on device connectivity. Choose AdGuard for ad-free browsing, Tailscale for networks.
- Tailscale 对比 Virtual Shield: Virtual Shield offers simple always-on VPN protection. Tailscale provides mesh networking. Virtual Shield is better for non-technical users who want basic VPN privacy.
- Tailscale 对比 StrongVPN: StrongVPN is a reliable traditional VPN with no data caps. Tailscale provides peer-to-peer mesh networking. Choose StrongVPN for browsing, Tailscale for server access.
- Tailscale 对比 AuraVPN: AuraVPN bundles VPN with identity protection and antivirus. Tailscale is a focused networking tool. Aura is better as an all-in-one security suite for personal safety.
- Tailscale 对阵 CyberGhost: CyberGhost has dedicated streaming and torrenting servers. Tailscale has no public servers — it connects your own devices. CyberGhost wins for entertainment, Tailscale for work.
- Tailscale 对比 McAfee VPN: McAfee VPN is part of a full security suite. Tailscale is a standalone mesh networking tool. McAfee is better for all-in-one protection, Tailscale for advanced networking.
- 尾规模网络与私有互联网接入: PIA offers open-source apps and deep customization. Tailscale offers zero-config mesh networking. PIA wins for privacy control, Tailscale for ease of device networking.
- 尾鳞对战神秘: Mysterium uses a decentralized peer network for anonymity. Tailscale uses a mesh network for your own devices. Mysterium is more anonymous, Tailscale is easier to use and manage.
- Tailscale VPN 与 SafeShell VPN 对比: SafeShell focuses on bypassing internet censorship. Tailscale focuses on private device networking. SafeShell is better for censored regions, Tailscale for remote access.
- Tailscale 对比 Oyster VPN: Oyster VPN offers lifetime access at a low one-time cost. Tailscale’s free plan covers most personal users. Oyster is cheaper long-term for basic VPN, Tailscale is better for networking.
立即开始使用 Tailscale
您已学会如何使用Tailscale的每一项主要功能:
- ✅ 企业版 VPN
- ✅ 安全远程访问
- ✅ 站点间联网
- ✅ 多云网络
- ✅ Kubernetes
- ✅ 边缘计算和物联网部署
- ✅ 云连接
- ✅ 保障人工智能安全
- ✅ 零信任网络
下一步: 选择一项功能,立即试用。
大多数人都是从安全远程访问开始的。
只需不到5分钟。
常见问题解答
How to actually use Tailscale?
Download the Tailscale app on your device, sign in with Google, Microsoft, GitHub, or Apple, and your device joins your tailnet. Install it on a second device and they can communicate directly. Run 尾规模地位 to see all connected devices. That’s it — no firewall rules or port forwarding needed.
What is Tailscale and how does it work?
Tailscale is a mesh VPN built on the WireGuard protocol. It creates a decentralized private network called a tailnet that connects your devices directly to each other. Tailscale assigns each device an IP address in the 100.x.x.x range and handles NAT traversal automatically. Traffic routes over the shortest path between peers — no central server sits in the middle.
我应该一直开着Tailscale吗?
Yes. Tailscale is designed to run in the background without affecting your device’s performance or internet speed. It only activates when you access another tailnet device. Leaving it on means your devices are always accessible from anywhere. Battery 影响 on phones is minimal since Tailscale uses very few resources when idle.
Tailscale 可以免费供个人使用吗?
Yes. Tailscale is free for personal use with the Personal plan. You get up to 3 users and 100 devices on a single tailnet. The free plan includes nearly every Tailscale feature. You can connect your phone, laptop, server, and Raspberry Pi without paying anything. No credit card is required to get started.
How to set up Tailscale at home?
Install Tailscale on every device you want to connect — your laptop, phone, and any home server. Sign in with the same account on each device. They all join your tailnet automatically. For accessing other devices on your home network, set up a subnet router on one always-on device like a Raspberry Pi.
Is Tailscale faster than WireGuard?
Tailscale is built on WireGuard, so the encryption speed is the same. The difference is in routing. Tailscale routes traffic over the shortest path possible — often a direct peer-to-peer connection. A standalone WireGuard setup usually routes through a single server. In practice, Tailscale can feel faster because packets take a more direct route.
What devices can run Tailscale?
Tailscale works on Windows, macOS, Linux, iOS, Android, and even Apple TV. It also runs on Raspberry Pi, Synology NAS, QNAP NAS, and various Linux-based routers. For Linux, a one-line script handles installation. Apple devices can download it from the App Store. Android users can get it from Google Play.
How do I start Tailscale?
On desktop, open the Tailscale app and click “Log In.” On a Linux machine, run tailscale up in your terminal. On mobile, open the app and toggle the connection on. Your device authenticates and joins your tailnet. You can then see all connected machines in the admin console or by running 尾规模地位.
人们使用Tailscale做什么?
People use Tailscale to access home servers remotely, share files between devices, connect to a Raspberry Pi from anywhere, secure cloud infrastructure, and replace corporate VPNs. Developers use it to access dev servers. IT teams use it for secure remote access to office networks. Home users love it for accessing media servers and smart home devices.
How do I set up a Tailscale subnet router?
Install Tailscale on a device connected to the subnet you want to share. Run tailscale up --advertise-routes=192.168.1.0/24 (use your actual subnet). Then go to the admin console and approve the route. Now any tailnet device can access machines on that subnet — even if those machines don’t have Tailscale installed.
How to set up Tailscale on Windows 10?
Download the Tailscale installer from tailscale.com/download. Run the installer and follow the setup wizard. Click the Tailscale icon in your system tray and sign in with your account. Your Windows computer joins your tailnet and appears in your machines list. You can now access it from any other connected device.
What does Tailscale actually do?
Tailscale builds a secure, encrypted mesh network between your devices. It lets your computer, phone, server, and IoT devices talk directly to each other from anywhere in the world. All connections are end-to-end encrypted using WireGuard. Tailscale handles all the complex networking — NAT traversal, key management, DNS — so you don’t have to.
Tailscale有哪些缺点?
Tailscale does not hide your IP address from websites. It cannot unblock streaming services or bypass geo-restrictions. The coordination server (control plane) is managed by Tailscale — if you need full self-hosting, you’ll need Headscale. Business plans can get expensive at $18/user/month for Premium features. Also, it’s not a replacement for a traditional VPN if you need online anonymity.
Tailscale会隐藏我的IP地址吗?
No. Tailscale does not hide your public IP address from websites you visit. It assigns private 100.x.x.x IP addresses for communication between your tailnet devices. If you want to mask your public IP, you can set up an exit node on your tailnet to route internet traffic through another device — but that’s not the same as a traditional VPN service.
Can Tailscale see my traffic?
No. Tailscale uses end-to-end encryption based on WireGuard. Your traffic goes directly between your devices — Tailscale’s servers never see the content. The coordination server only handles key exchange and device authentication. Even if Tailscale uses DERP relay servers, the traffic is still encrypted and Tailscale cannot read it.