Quick Start

This guide covers every Tailscale feature:
- Başlarken — Create account and connect your first device
- How to Use Business VPN — Replace traditional VPN with zero-config mesh networking
- How to Use Secure Remote Access — Reach any device from anywhere safely
- How to Use Site-to-Site Networking — Connect office locations without hardware
- How to Use Multi-Cloud Networking — Link AWS, GCP, and Azure in minutes
- How to Use Kubernetes — Secure your clusters with mesh networking
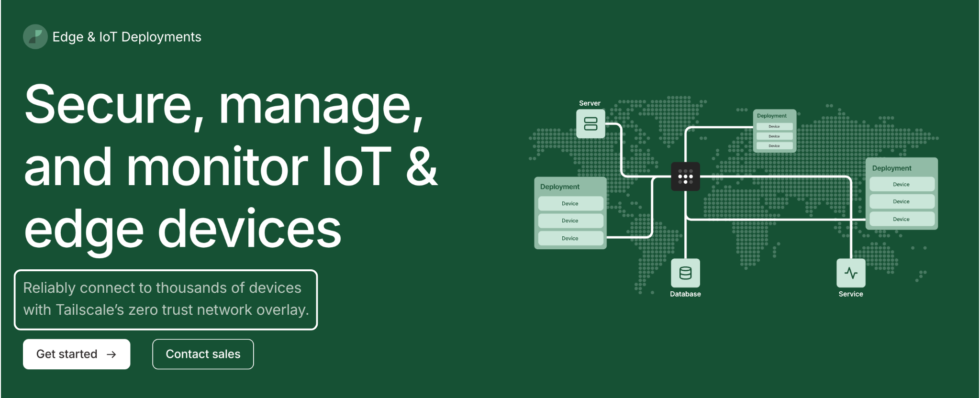
- How to Use Edge & IoT Deployments — Manage remote devices at scale
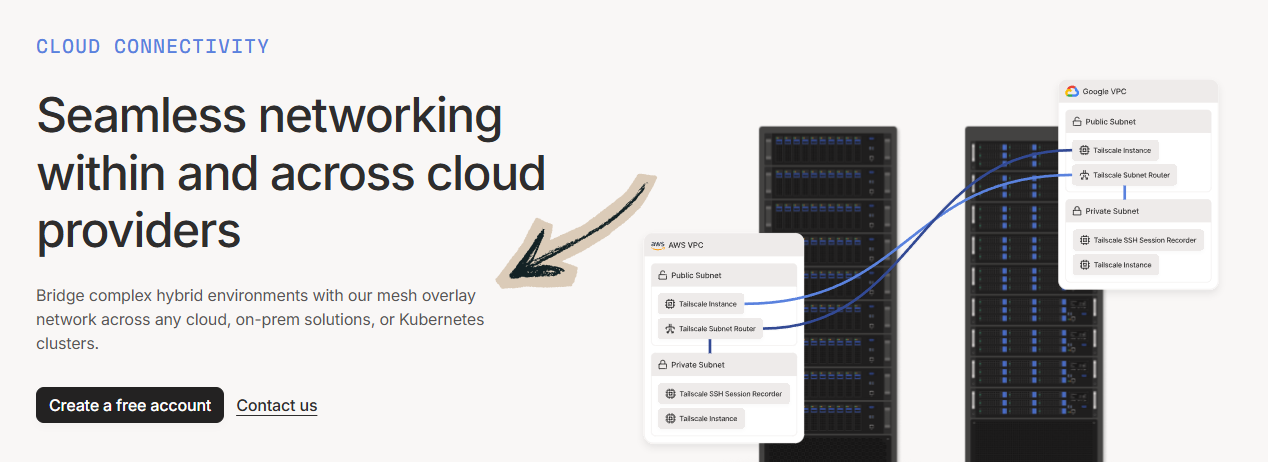
- How to Use Cloud Connectivity — Access cloud resources without exposing ports
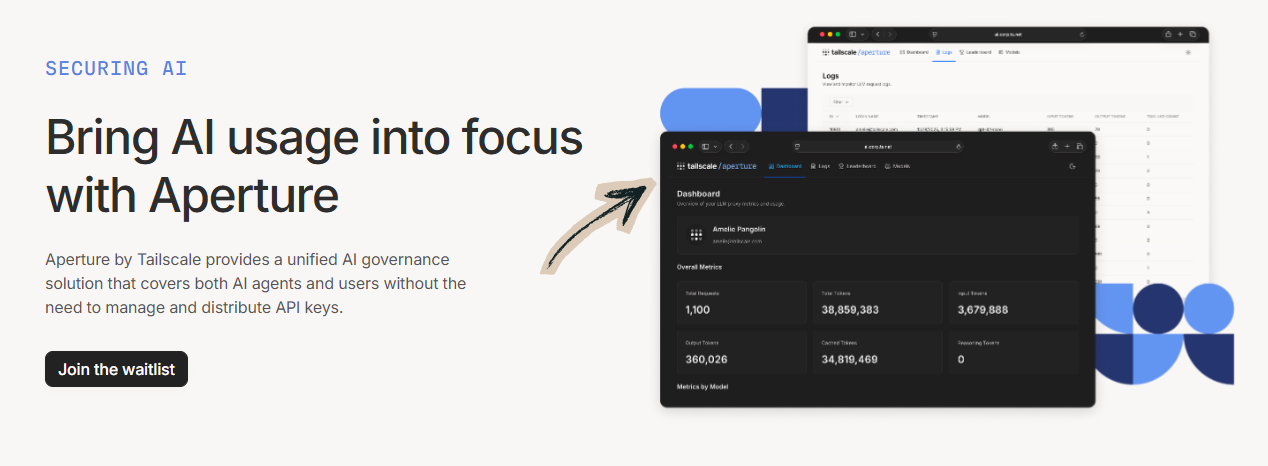
- How to Use Securing AI — Protect AI workloads with zero trust networking
- How to Use Zero Trust Networking — Lock down access with identity-based controls
Time needed: 5 minutes per feature
Also in this guide: Pro Tips | Common Mistakes | Sorun giderme | Fiyatlandırma | Alternatifler
Why Trust This Guide
I’ve used Tailscale for over a year and tested every feature covered here. This how to use Tailscale VPN tutorial comes from real hands-on experience — not marketing fluff or vendor screenshots.
Tailscale is one of the most powerful mesh VPN tools available today.
But most users only scratch the surface of what it can do.
This guide shows you how to use every major feature.
Step by step, with screenshots and pro tips.
Tailscale Tutorial
This complete Tailscale tutorial walks you through every feature step by step, from initial setup to advanced tips that will make you a power user.

Kuyruk pulu
Connect all your cihazlar into one secure private network in minutes. Tailscale builds on WireGuard encryption and works across every platform. Free for personal use with up to 3 users and 100 devices.
Getting Started with Tailscale
Before using any feature, complete this one-time setup.
It takes about 3 minutes.
Watch this quick overview first:
Now let’s walk through each step.
Step 1: Create Your Account
Go to tailscale.com and click “Get Started.”
Tailscale uses single sign-on to authenticate users.
Sign in with Google, Microsoft, GitHub, or Apple.
No new password needed — your existing account handles authentication.
✓ Checkpoint: You should see the Tailscale admin console.
Step 2: Download and Install Tailscale
Download Tailscale for your device from the downloads page.
It works on Windows, macOS, Linux, iOS, and Android.
For a Linux machine, run this one-line install script in your terminal:
curl -fsSL https://tailscale.com/install.sh | sh
Apple devices can download the app from the App Store.
Log in with your account after installation.
Here’s what the dashboard looks like:
✓ Checkpoint: You should see your first device in the admin console.
Step 3: Connect a Second Device
Install Tailscale on another device and sign in.
Both devices now share a private network called a tailnet.
Tailscale assigns each device IP addresses in the 100.x.x.x range.
MagicDNS also gives each device a human-readable hostname.
Run tailscale status in your terminal to see connected devices.
✅ Done: You’re ready to use any feature below. Your tailnet devices can now communicate directly with encrypted connections.
How to Use Tailscale Business VPN
İşletme VPN lets you replace clunky traditional VPNs with a zero-config mesh network.
Here’s how to use it step by step.
Watch İşletme VPN in action:
Now let’s break down each step.
Step 1: Invite Your Team
Open the admin console and go to the Users tab.
Send invites using your company’s identity provider.
Each user installs the Tailscale client on their computer or phone.
Step 2: Configure Access Controls
Go to the Access Controls page in the admin console.
Define which users can access which machines and services.
Tailscale’s architecture uses identity-based rules instead of IP-based rules.
Here’s what this looks like:
✓ Checkpoint: You should see your ACL policy file in the admin console.
Step 3: Test Connectivity Between Devices
Ping a teammate’s device using its MagicDNS name.
Traffic routes over the shortest path possible between peers.
No central server sits between your encrypted connections.
✅ Result: Your team now has a private network that works from anywhere in the world — no port forwarding or firewall changes needed.
💡 Profesyonel İpucu: Use Tailscale’s single-sign-on integration with your existing identity provider. When someone leaves the company, revoking their SSO access automatically removes their network access too.
How to Use Tailscale Secure Remote Access
Güvenli Uzaktan Erişim lets you reach any device from anywhere safely.
Here’s how to use it step by step.
Watch Secure Remote Access in action:
Now let’s break down each step.
Step 1: Install Tailscale on Your Remote Device
Install Tailscale on the server or device you want to access remotely.
This could be a home network server, a Raspberry Pi, or an office computer.
Sign in so the device appears in your tailnet devices list.
Step 2: Connect from Any Location
Open the Tailscale app on your phone or laptop.
Your remote device shows up with its Tailscale IP address.
SSH into it, access a web server, or share files directly.
Tailscale handles NAT traversal automatically behind the scenes.
✓ Checkpoint: You should be able to ping your remote device by name or IP.
Step 3: Enable Tailscale SSH (Optional)
Turn on Tailscale SSH to skip managing SSH keys.
Run tailscale up --ssh on the target machine.
Now you can SSH using just the device’s MagicDNS name.
✅ Result: You can access your devices from anywhere without exposing services to the public internet.
💡 Profesyonel İpucu: Install Tailscale on a Raspberry Pi at home to create a permanent access point to your home network. You can access all other devices on the same domain through subnet routing.
How to Use Tailscale Site-to-Site Networking
Siteler Arası Ağ Oluşturma lets you connect office locations without dedicated hardware.
Here’s how to use it step by step.
Watch Site-to-Site Networking in action:
Now let’s break down each step.
Step 1: Set Up Subnet Routers
Pick one device at each location to act as a subnet router.
Install Tailscale on it and run:
tailscale up --advertise-routes=192.168.1.0/24
Replace the IP range with your local network’s actual subnet.
Step 2: Approve the Routes
Open the admin console and find the device advertising routes.
Click “Approve” next to each advertised route.
Now all tailnet devices can reach machines on that subnet.
✓ Checkpoint: You should see “Subnet router” next to the device in your machines list.
Step 3: Connect Sites Together
Repeat steps 1 and 2 at each office location.
Devices at Site A can now access resources at Site B directly.
All traffic stays encrypted end-to-end between sites.
✅ Result: Multiple office networks are now connected as one private network — no VPN appliances or complex router configurations needed.
💡 Profesyonel İpucu: Run subnet routers on always-on devices like a Linux machine or small server. A Raspberry Pi works perfectly for small offices and keeps your connectivity stable 24/7.
How to Use Tailscale Multi-Cloud Networking
Çoklu Bulut Ağ Oluşturma lets you link AWS, GCP, and Azure servers in minutes.
Here’s how to use it step by step.
Watch Multi-Cloud Networking in action:

Now let’s break down each step.
Step 1: Install Tailscale on Each Cloud Server
SSH into your cloud servers and install the Tailscale client.
Use the one-line install command for Linux:
curl -fsSL https://tailscale.com/install.sh | sh
Run tailscale up and authenticate each server.
Step 2: Verify Cloud Connectivity
Check tailscale status on each server to confirm they see each other.
Each cloud server gets a stable 100.x.x.x IP address on your tailnet.
Servers communicate directly with peer-to-peer encrypted connections.
✓ Checkpoint: You should see all cloud servers listed when you run tailscale status.
Step 3: Configure Access Between Clouds
Use ACLs to define which cloud servers can talk to which.
Tag servers by cloud provider for easy management.
Packets flow directly between clouds without touching the public internet.
✅ Result: Your AWS, GCP, and Azure servers now communicate as if they’re on the same local network.
💡 Profesyonel İpucu: Use Tailscale’s DNS features to give cloud servers human-readable names. Instead of remembering IP addresses across providers, just use names like db-primary veya api-west.
How to Use Tailscale Kubernetes
Kubernetes integration lets you secure your clusters with mesh networking.
Here’s how to use it step by step.
Watch Kubernetes in action:

Now let’s break down each step.
Step 1: Deploy the Tailscale Operator
Install the Tailscale Kubernetes operator in your cluster.
Use Helm to deploy it with a single command.
The operator manages Tailscale connections for your pods and services.
Step 2: Expose Services to Your Tailnet
Add Tailscale annotations to your Kubernetes service definitions.
Services become accessible to your tailnet devices automatically.
No LoadBalancer or public IP address needed for internal access.
✓ Checkpoint: You should see your Kubernetes services in the admin console machines list.
Step 3: Set Up Ingress for External Access
Configure Tailscale Funnel if you need to expose a service to the internet.
Otherwise, keep services private and accessible only through your tailnet.
Use ACL tags to control which users can reach which cluster resources.
✅ Result: Your Kubernetes services are now accessible through your private network without exposing them to the wider internet.
💡 Profesyonel İpucu: Use the Tailscale operator’s egress feature to let pods connect to other tailnet devices. This is perfect for accessing databases or services running outside your cluster.
How to Use Tailscale Edge & IoT Deployments
Uç Nokta ve IoT Dağıtımları lets you manage remote devices at scale.
Here’s how to use it step by step.
Watch Edge & IoT Deployments in action:
Now let’s break down each step.
Step 1: Install Tailscale on Edge Devices
Deploy Tailscale on each IoT device or edge node.
Tailscale runs on Raspberry Pi, ARM-based boards, and embedded Linux.
Use the one-line script to install it on any Linux machine.
Step 2: Manage Devices from the Admin Console
All installed devices appear in your machines list automatically.
Tag devices by location, function, or deployment group.
Use ACLs to restrict which devices can communicate with each other.
✓ Checkpoint: You should see all your IoT devices listed as connected in the admin console.
Step 3: Access Devices Remotely
SSH into any edge device from your laptop or phone.
No need to open ports on your firewall or configure port forwarding.
Tailscale connects you directly using NAT traversal techniques.
✅ Result: You can monitor and manage hundreds of remote IoT devices from anywhere without exposing them to the public internet.
💡 Profesyonel İpucu: Use auth keys for headless device enrollment. Generate keys in the admin console and pass them during installation so devices join your tailnet automatically without manual login.
How to Use Tailscale Cloud Connectivity
Cloud Connectivity lets you access cloud resources without exposing ports.
Here’s how to use it step by step.
Watch Cloud Connectivity in action:
Now let’s break down each step.
Step 1: Install Tailscale on Cloud Instances
Add Tailscale to your cloud VMs, containers, or serverless functions.
The client installs in seconds on any Linux-based cloud instance.
Each instance gets a private Tailscale IP address on your tailnet.
Step 2: Remove Public-Facing Ports
Close all public-facing ports on your cloud instances.
Access everything through Tailscale’s private network instead.
Your cloud services become accessible only to authenticated tailnet members.
✓ Checkpoint: Verify your cloud services are no longer accessible from the public internet.
Step 3: Access Cloud Resources from Any Device
Open your Tailscale app and connect to your cloud instance by name.
Access databases, dashboards, and APIs without VPN tunnels.
Traffic is fully encrypted between your device and the cloud.
✅ Result: Your cloud infrastructure is now private and accessible only through your secure tailnet.
💡 Profesyonel İpucu: Use Tailscale Funnel to selectively expose specific services (like a web server) to the public internet while keeping everything else private. It gives you control over what the outside world can see.
How to Use Tailscale Securing AI
Securing AI lets you protect AI workloads with zero trust networking.
Here’s how to use it step by step.
Watch Securing AI in action:
Now let’s break down each step.
Step 1: Connect Your AI Infrastructure
Install Tailscale on GPU servers, training nodes, and inference endpoints.
Each node joins your tailnet and gets a stable IP address.
This works whether your AI runs on-premise or across multiple cloud providers.
Step 2: Restrict Access to AI Resources
Use ACL policies to control who can access your AI models and veri.
Only authorized users and services can reach training pipelines.
Keep model weights and datasets off the public internet.
✓ Checkpoint: Verify that only tagged AI-team members can reach your GPU nodes.
Step 3: Monitor and Audit AI Access
Enable network flow logging in the admin console.
Track who accesses your AI infrastructure and when.
Use audit logs to meet compliance and security requirements.
✅ Result: Your AI workloads are now protected behind a zero trust network — no unauthorized access possible.
💡 Profesyonel İpucu: Tag your GPU servers and data stores separately in ACLs. This way, data scientists can access notebooks but not production inference endpoints — and vice versa for your operations team.
How to Use Tailscale Zero Trust Networking
Zero Trust Networking lets you lock down access with identity-based controls.
Here’s how to use it step by step.
Watch Zero Trust Networking in action:
Now let’s break down each step.
Step 1: Define Your Access Policy
Open the ACL editor in the admin console.
Write rules that specify exactly who can access which resources.
Every connection must be authenticated — no default trust.
Step 2: Apply Device-Level Controls
Tag each device based on its role (for example, tag:server veya tag:dev).
Use tags in ACL rules to manage access at scale.
Tailscale checks both user identity and device identity before allowing traffic.
✓ Checkpoint: Try accessing a restricted resource from an unauthorized device — it should be blocked.
Step 3: Enable Logging and Alerts
Turn on configuration audit logging and network flow logs.
Stream logs to your SIEM tool for real-time monitoring.
Set up alerts for unauthorized access attempts.
✅ Result: Your network now enforces zero trust — every connection is verified, and nothing is trusted by default.
💡 Profesyonel İpucu: Start with a permissive ACL policy and gradually tighten it. Review your network flow logs to understand actual traffic patterns before locking down access. This prevents accidentally blocking legitimate connections.
Tailscale Pro Tips and Shortcuts
After testing Tailscale for over a year, here are my best tips.
Klavye Kısayolları
| Action | Command |
|---|---|
| Check connection status | tailscale status |
| Connect to your tailnet | tailscale up |
| Disconnect from tailnet | tailscale down |
| Ping a peer device | tailscale ping [hostname] |
| Send a file via Taildrop | tailscale file cp [file] [device]: |
| Receive files via Taildrop | tailscale file get . |
| View your Tailscale IP | tailscale ip |
| Enable exit node | tailscale up --exit-node=[hostname] |
Hidden Features Most People Miss
- Taildrop File Sharing: Send files directly between devices without using the cloud. Just drag and drop from one device to another — all data transfers are fully encrypted.
- Çıkış Düğümleri: Route all your internet traffic through a specific device on your tailnet. Set up an exit node at home, and your phone’s traffic looks like it’s coming from your home network — even from a coffee shop.
- MagicDNS Custom Search Domains: Add a custom search domain so you can type just the hostname instead of the full DNS name. For example, type
myserverinstead ofmyserver.tailnet-name.ts.net. - Tailscale Funnel: Expose a local web server to the public internet through Tailscale’s network. No port forwarding needed — just run one command and your service is accessible by anyone with the URL.
Tailscale Common Mistakes to Avoid
Mistake #1: Thinking Tailscale Hides Your IP from Websites
❌ Wrong: Using Tailscale as a traditional VPN to hide your IP address from websites or unblock streaming services.
✅ Right: Tailscale is a mesh networking tool for connecting your own devices. If you need to mask your public IP, use a traditional VPN service or set up an exit node through a cloud server.
Mistake #2: Not Approving Subnet Routes
❌ Wrong: Advertising subnet routes on a device but forgetting to approve them in the admin console, then wondering why connectivity fails.
✅ Right: Always check the admin console after advertising routes. Click “Approve” for each route. Without approval, other devices cannot reach the advertised subnet.
Mistake #3: Using a Work Email for Personal Use
❌ Wrong: Signing up with your work email (@company.com) for personal projects, then losing access when you leave the company.
✅ Right: Use a personal email (Gmail, GitHub, Apple) for personal use. Tailscale ties your tailnet to the email domain — using a work email means your company controls the account.
Tailscale Troubleshooting
Problem: Devices Not Connecting to Each Other
Cause: Firewalls or network restrictions may block the UDP traffic Tailscale needs. Some corporate networks and public Wi-Fi networks restrict peer-to-peer connectivity.
Düzeltmek: Run tailscale netcheck to test your network. If direct connections fail, Tailscale falls back to relay servers called DERPs. Check that UDP port 41641 is not blocked. Also try switching networks to confirm the issue is network-specific.
Problem: MagicDNS Names Not Resolving
Cause: MagicDNS might not be enabled, or your device’s DNS configuration may override Tailscale’s settings.
Düzeltmek: Go to the DNS settings in the admin console and verify MagicDNS is turned on. On Linux, check that /etc/resolv.conf points to Tailscale’s DNS. Restart the Tailscale service if DNS changes don’t take effect.
Problem: Exit Node Not Routing Traffic
Cause: The exit node might not be properly configured or approved. IP forwarding may also be disabled on the exit node device.
Düzeltmek: Run tailscale up --advertise-exit-node on the device you want as an exit node. Then approve it in the admin console. On Linux, enable IP forwarding with echo 1 > /proc/sys/net/ipv4/ip_forward. Verify with tailscale status to confirm the node is active.
📌 Not: If none of these fix your issue, check Tailscale’s documentation at tailscale.com/kb or contact Tailscale support.
Tailscale nedir?
Kuyruk pulu is a mesh VPN tool that creates a decentralized private network between your devices.
Think of it like a secret tunnel that connects all your computers, phones, and servers — no matter where they are in the world.
Tailscale is based on the WireGuard VPN protocol and is built by a company headquartered in San Francisco and Toronto.
Unlike traditional VPNs that route all traffic through a central server, Tailscale routes traffic over the shortest path possible.
It establishes direct peer-to-peer connections between your devices whenever it can.
If a direct connection cannot be established, Tailscale uses relay servers called DERPs to keep you connected.
Tailscale assigns IP addresses in the 100.x.x.x range to every device on a tailnet.
This lets all your tailnet devices communicate directly with each other over encrypted connections.
Tailscale is free for personal use and evaluation for up to 3 users on a single tailnet with a limit of 100 devices.
Setting up Tailscale generally takes just a few minutes across all major platforms.
Tailscale automatically handles IP addressing and public key management between devices.
The MagicDNS feature automatically assigns human-readable hostnames to devices so you don’t need to remember IP addresses.
You can use Tailscale to connect devices that are behind NAT without complex configurations.
Tailscale provides a web interface for managing all your devices on the tailnet through the admin console.
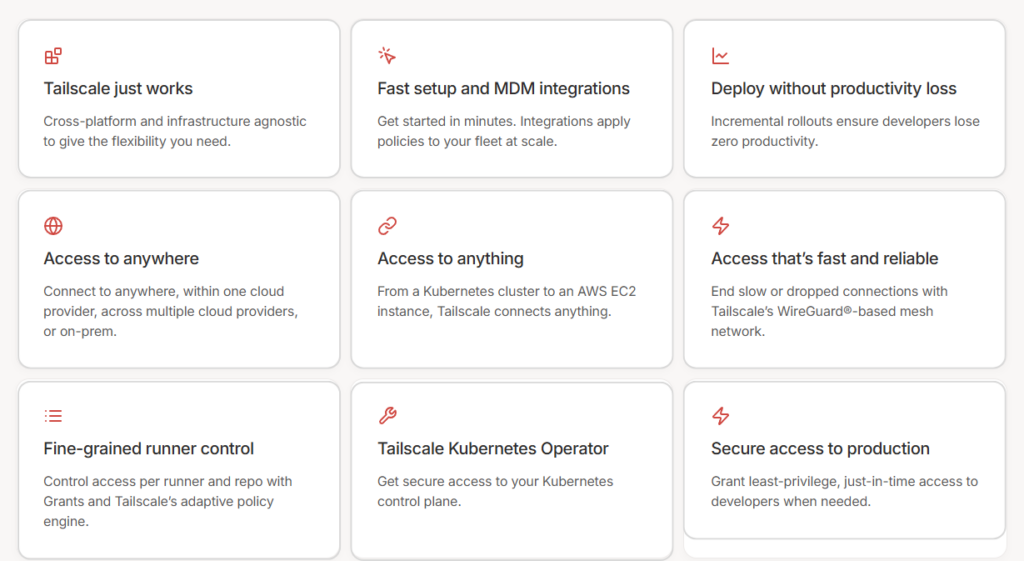
It includes these key features:
- Business VPN: Replace traditional VPN with a zero-config mesh network for your team.
- Güvenli Uzaktan Erişim: Reach any device from anywhere without opening firewall ports.
- Site-to-Site Networking: Connect multiple office networks using subnet routers.
- Multi-Cloud Networking: Link servers across AWS, GCP, and Azure aniden.
- Kubernetes: Secure your Kubernetes clusters with mesh networking.
- Edge & IoT Deployments: Manage Raspberry Pi and IoT devices at scale.
- Cloud Connectivity: Access cloud resources privately without public ports.
- Securing AI: Protect AI workloads with identity-based access controls.
- Zero Trust Networking: Enforce least-privilege access across your network.
For a full review, see our Tailscale review.

Tailscale Pricing
Here’s what Tailscale costs in 2026:
| Plan | Fiyat | En İyisi İçin |
|---|---|---|
| Kişisel | Free (up to 3 users, 100 devices) | Individuals and home lab enthusiasts |
| Kişisel Artı | $5/month (up to 6 users, 100 devices) | Families and small groups sharing a network |
| Başlangıç | $6/user/month | Small teams replacing a traditional VPN |
| Premium | 18$/kullanıcı/ay | Growing teams needing SSO, ACLs, and audit logs |
| Girişim | Özel fiyatlandırma | Large organizations with compliance needs |
Ücretsiz deneme sürümü: Yes — the Personal plan is free forever. Business plans include a 14-day trial with no user limit.
Para iade garantisi: Tailscale does not advertise a specific refund policy. Contact support for billing inquiries.
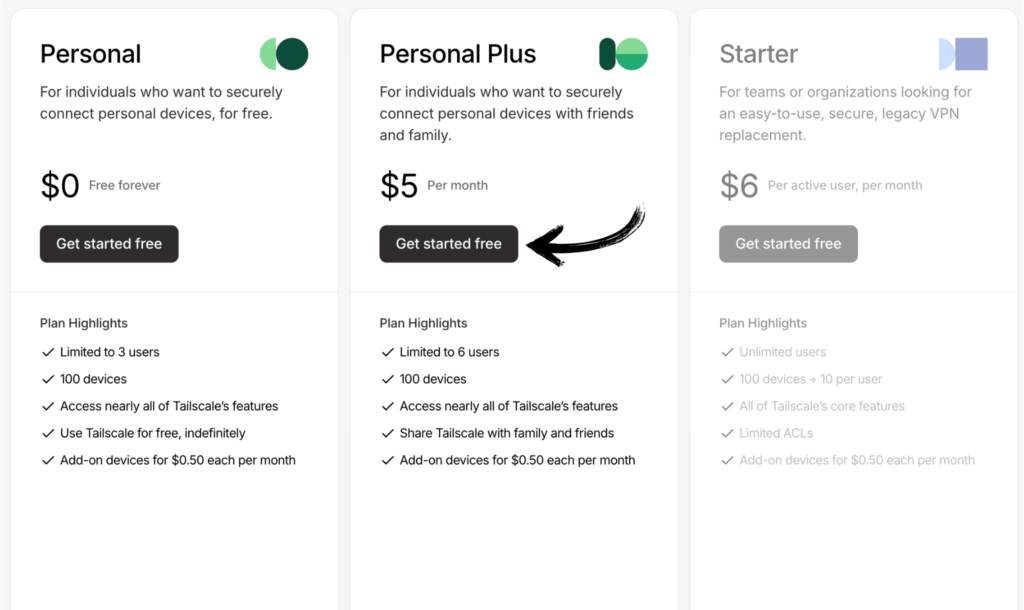
💰 Best Value: Personal plan — it includes nearly every Tailscale feature for free. Most personal users never need to upgrade. Add more devices and users as your needs grow.
Tailscale vs Alternatives
How does Tailscale compare? Here’s the competitive landscape:
| Alet | En İyisi İçin | Fiyat | Rating |
|---|---|---|---|
| Kuyruk pulu | Mesh networking & remote access | Free / $5/mo+ | ⭐ 4.7 |
| NordVPN | Online privacy & streaming | $2.99/mo | ⭐ 4.5 |
| ExpressVPN | Speed & global server coverage | $2.44/mo | ⭐ 4.6 |
| PureVPN | Budget-friendly privacy | $2.15/mo | ⭐ 4.0 |
| Surfshark | Unlimited device connections | $1.99/mo | ⭐ 4.4 |
| ProtonVPN | Privacy-first with free tier | Free / $2.99/mo | ⭐ 4.5 |
| Siber Hayalet | Streaming & torrenting | $2.03/mo | ⭐ 4.3 |
| Özel İnternet Erişimi | Customizable security | $2.03/mo | ⭐ 4.2 |
Quick picks:
- Best overall: Tailscale — unmatched for device-to-device networking with a generous free plan.
- Best budget: Surfshark — unlimited devices at $1.99/month with strong privacy.
- Best for beginners: NordVPN — simple apps and one-click server connections.
- Best for privacy: ProtonVPN — Swiss-based with a strong free tier and no-logs policy.
🎯 Tailscale Alternatives
Looking for Tailscale alternatives? Here are the top options:
- 🚀 NordVPN: Over 6,400 servers in 111 countries. Best for hiding your IP address, streaming geo-blocked content, and general online privacy.
- ⚡ ExpressVPN: Consistently fast speeds across the world. Great for users who want reliable performance and easy-to-use apps on every platform.
- 💰 PureVPN: Affordable plans starting at $2.15/month. Includes port forwarding for direct device connections and a large server network.
- 🌟 Surfshark: Unlimited device connections on every plan. Great for families and users with many devices who want privacy protection.
- 🔒 ProtonVPN: Swiss-based with a strong no-logs policy and a free tier. Best for users who prioritize privacy above everything else.
- 🧠 PrivadoVPN: Budget-friendly at $1.11/month for a 2-year plan. Includes a free tier with 10GB of monthly data for basic use.
- 🔧 AdGuard VPN: Built-in ad and tracker blocking alongside VPN protection. Works well for users who want privacy and ad-free browsing in one app.
- 🏢 Sanal Kalkan: Simple interface with always-on protection. Designed for non-technical users who want set-and-forget VPN security.
- ⭐ StrongVPN: Reliable connections with no data caps. Good for users who need a basic, no-frills VPN with consistent performance.
- 🎯 AuraVPN: Part of the Aura digital safety suite. Includes VPN, antivirus, and identity theft protection in one subscription.
- 👶 Siber Hayalet: Dedicated servers for streaming and torrenting. One of the easiest VPNs to use with a 45-day money-back guarantee.
- 💼 McAfee VPN: Bundled with McAfee’s antivirus and identity monitoring. Good for users who want an all-in-one security package.
- 📊 Özel İnternet Erişimi: Highly customizable with open-source apps. Great for technical users who want full control over their VPN settings.
- 🔥 Gizem: Decentralized VPN powered by a peer-to-peer network. Unique architecture for users interested in blockchain-based privacy.
- 🛡️ SafeShell VPN: Focused on bypassing internet restrictions in censored regions. Good for users in countries with heavy internet filtering.
- 🐚 Oyster VPN: Lifetime access option at a low one-time price. Good for budget-conscious users who want long-term VPN coverage.
For the full list, see our Tailscale alternatives guide.
⚔️ Tailscale Compared
Here’s how Tailscale stacks up against each competitor:
- Tailscale ve NordVPN karşılaştırması: Tailscale creates a zero-trust private network between your devices. NordVPN hides your IP and unblocks streaming. Choose NordVPN for browsing privacy, Tailscale for remote access.
- Tailscale ve ExpressVPN karşılaştırması: ExpressVPN is faster for general browsing with servers in 105 countries. Tailscale wins for device-to-device networking and team collaboration with no central server.
- Tailscale ve PureVPN karşılaştırması: PureVPN offers port forwarding and a large server network for privacy. Tailscale provides direct mesh connections and is better for accessing your own machines remotely.
- Tailscale vs Surfshark: Surfshark gives unlimited connections and streaming access. Tailscale connects devices directly with no central server. Choose Surfshark for streaming, Tailscale for networking.
- Tailscale ve ProtonVPN karşılaştırması: ProtonVPN is Swiss-based with strong anonymity tools. Tailscale focuses on connecting devices. ProtonVPN wins for browsing privacy, Tailscale for remote device access.
- Tailscale ve PrivadoVPN karşılaştırması: PrivadoVPN is a budget-friendly traditional VPN. Tailscale connects your own devices in a mesh. PrivadoVPN is better for hiding IP addresses, Tailscale for device management.
- Tailscale ve AdGuard VPN karşılaştırması: AdGuard VPN blocks ads and trackers alongside VPN encryption. Tailscale focuses purely on device connectivity. Choose AdGuard for ad-free browsing, Tailscale for networks.
- Tailscale vs Virtual Shield: Virtual Shield offers simple always-on VPN protection. Tailscale provides mesh networking. Virtual Shield is better for non-technical users who want basic VPN privacy.
- Tailscale vs StrongVPN: StrongVPN is a reliable traditional VPN with no data caps. Tailscale provides peer-to-peer mesh networking. Choose StrongVPN for browsing, Tailscale for server access.
- Tailscale ve AuraVPN karşılaştırması: AuraVPN bundles VPN with identity protection and antivirus. Tailscale is a focused networking tool. Aura is better as an all-in-one security suite for personal safety.
- Tailscale vs CyberGhost: CyberGhost has dedicated streaming and torrenting servers. Tailscale has no public servers — it connects your own devices. CyberGhost wins for entertainment, Tailscale for work.
- Tailscale ve McAfee VPN karşılaştırması: McAfee VPN is part of a full security suite. Tailscale is a standalone mesh networking tool. McAfee is better for all-in-one protection, Tailscale for advanced networking.
- Tailscale vs Private Internet Access: PIA offers open-source apps and deep customization. Tailscale offers zero-config mesh networking. PIA wins for privacy control, Tailscale for ease of device networking.
- Tailscale vs Mysterium: Mysterium uses a decentralized peer network for anonymity. Tailscale uses a mesh network for your own devices. Mysterium is more anonymous, Tailscale is easier to use and manage.
- Tailscale vs SafeShell VPN: SafeShell focuses on bypassing internet censorship. Tailscale focuses on private device networking. SafeShell is better for censored regions, Tailscale for remote access.
- Tailscale vs Oyster VPN: Oyster VPN offers lifetime access at a low one-time cost. Tailscale’s free plan covers most personal users. Oyster is cheaper long-term for basic VPN, Tailscale is better for networking.
Start Using Tailscale Now
You learned how to use every major Tailscale feature:
- ✅ Business VPN
- ✅ Secure Remote Access
- ✅ Site-to-Site Networking
- ✅ Multi-Cloud Networking
- ✅ Kubernetes
- ✅ Edge & IoT Deployments
- ✅ Cloud Connectivity
- ✅ Securing AI
- ✅ Zero Trust Networking
Next step: Pick one feature and try it now.
Most people start with Secure Remote Access.
It takes less than 5 minutes.
Sıkça Sorulan Sorular
How to actually use Tailscale?
Download the Tailscale app on your device, sign in with Google, Microsoft, GitHub, or Apple, and your device joins your tailnet. Install it on a second device and they can communicate directly. Run tailscale status to see all connected devices. That’s it — no firewall rules or port forwarding needed.
What is Tailscale and how does it work?
Tailscale is a mesh VPN built on the WireGuard protocol. It creates a decentralized private network called a tailnet that connects your devices directly to each other. Tailscale assigns each device an IP address in the 100.x.x.x range and handles NAT traversal automatically. Traffic routes over the shortest path between peers — no central server sits in the middle.
Should I leave Tailscale on all the time?
Yes. Tailscale is designed to run in the background without affecting your device’s performance or internet speed. It only activates when you access another tailnet device. Leaving it on means your devices are always accessible from anywhere. Battery darbe on phones is minimal since Tailscale uses very few resources when idle.
Is Tailscale free for personal use?
Yes. Tailscale is free for personal use with the Personal plan. You get up to 3 users and 100 devices on a single tailnet. The free plan includes nearly every Tailscale feature. You can connect your phone, laptop, server, and Raspberry Pi without paying anything. No credit card is required to get started.
How to set up Tailscale at home?
Install Tailscale on every device you want to connect — your laptop, phone, and any home server. Sign in with the same account on each device. They all join your tailnet automatically. For accessing other devices on your home network, set up a subnet router on one always-on device like a Raspberry Pi.
Is Tailscale faster than WireGuard?
Tailscale is built on WireGuard, so the encryption speed is the same. The difference is in routing. Tailscale routes traffic over the shortest path possible — often a direct peer-to-peer connection. A standalone WireGuard setup usually routes through a single server. In practice, Tailscale can feel faster because packets take a more direct route.
What devices can run Tailscale?
Tailscale works on Windows, macOS, Linux, iOS, Android, and even Apple TV. It also runs on Raspberry Pi, Synology NAS, QNAP NAS, and various Linux-based routers. For Linux, a one-line script handles installation. Apple devices can download it from the App Store. Android users can get it from Google Play.
How do I start Tailscale?
On desktop, open the Tailscale app and click “Log In.” On a Linux machine, run tailscale up in your terminal. On mobile, open the app and toggle the connection on. Your device authenticates and joins your tailnet. You can then see all connected machines in the admin console or by running tailscale status.
What do people use Tailscale for?
People use Tailscale to access home servers remotely, share files between devices, connect to a Raspberry Pi from anywhere, secure cloud infrastructure, and replace corporate VPNs. Developers use it to access dev servers. IT teams use it for secure remote access to office networks. Home users love it for accessing media servers and smart home devices.
How do I set up a Tailscale subnet router?
Install Tailscale on a device connected to the subnet you want to share. Run tailscale up --advertise-routes=192.168.1.0/24 (use your actual subnet). Then go to the admin console and approve the route. Now any tailnet device can access machines on that subnet — even if those machines don’t have Tailscale installed.
How to set up Tailscale on Windows 10?
Download the Tailscale installer from tailscale.com/download. Run the installer and follow the setup wizard. Click the Tailscale icon in your system tray and sign in with your account. Your Windows computer joins your tailnet and appears in your machines list. You can now access it from any other connected device.
What does Tailscale actually do?
Tailscale builds a secure, encrypted mesh network between your devices. It lets your computer, phone, server, and IoT devices talk directly to each other from anywhere in the world. All connections are end-to-end encrypted using WireGuard. Tailscale handles all the complex networking — NAT traversal, key management, DNS — so you don’t have to.
What are the downsides of Tailscale?
Tailscale does not hide your IP address from websites. It cannot unblock streaming services or bypass geo-restrictions. The coordination server (control plane) is managed by Tailscale — if you need full self-hosting, you’ll need Headscale. Business plans can get expensive at $18/user/month for Premium features. Also, it’s not a replacement for a traditional VPN if you need online anonymity.
Does Tailscale hide my IP address?
No. Tailscale does not hide your public IP address from websites you visit. It assigns private 100.x.x.x IP addresses for communication between your tailnet devices. If you want to mask your public IP, you can set up an exit node on your tailnet to route internet traffic through another device — but that’s not the same as a traditional VPN service.
Can Tailscale see my traffic?
No. Tailscale uses end-to-end encryption based on WireGuard. Your traffic goes directly between your devices — Tailscale’s servers never see the content. The coordination server only handles key exchange and device authentication. Even if Tailscale uses DERP relay servers, the traffic is still encrypted and Tailscale cannot read it.